Let devs be devs without sacrificing security
Andrew McNamara; Red Hat
Devs need to be protected from threats
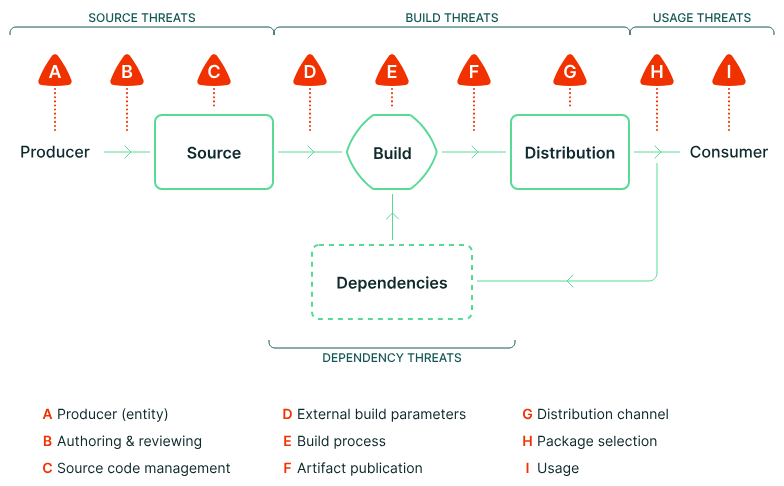
Source: https://slsa.dev/spec/v1.1/threats-overview
What does it mean to be a developer?
Build off of open source software
Troubleshoot their builds
Explore new problem spaces and solutions
Use tooling that is supportive not disruptive
Devs want to easily build artifacts

Devs want to troubleshoot builds

Devs want to explore new tech

Devs don’t need to be this unhappy
SLSA Build L3:
Harden the build platform
Generate provenance

Foundation Platform
Kubernetes provides RBAC, containerization, and namespace isolation. Tekton provides the pipeline execution framework.
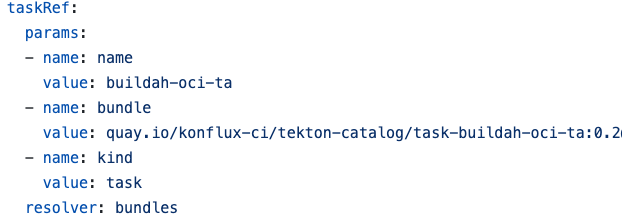
Secure Task Library
A library of tasks providing common and critical functions which need to be secure and auditable.
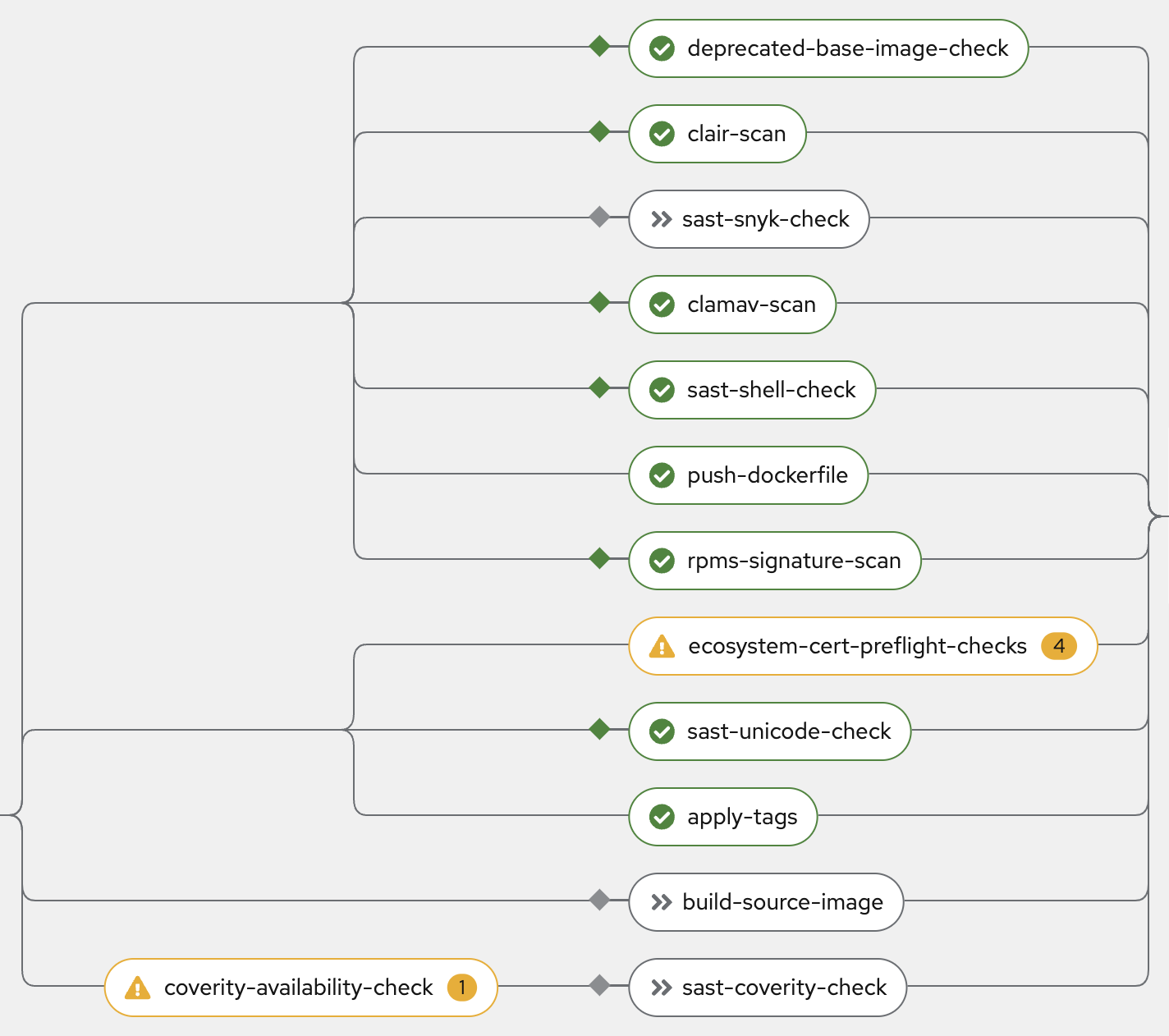
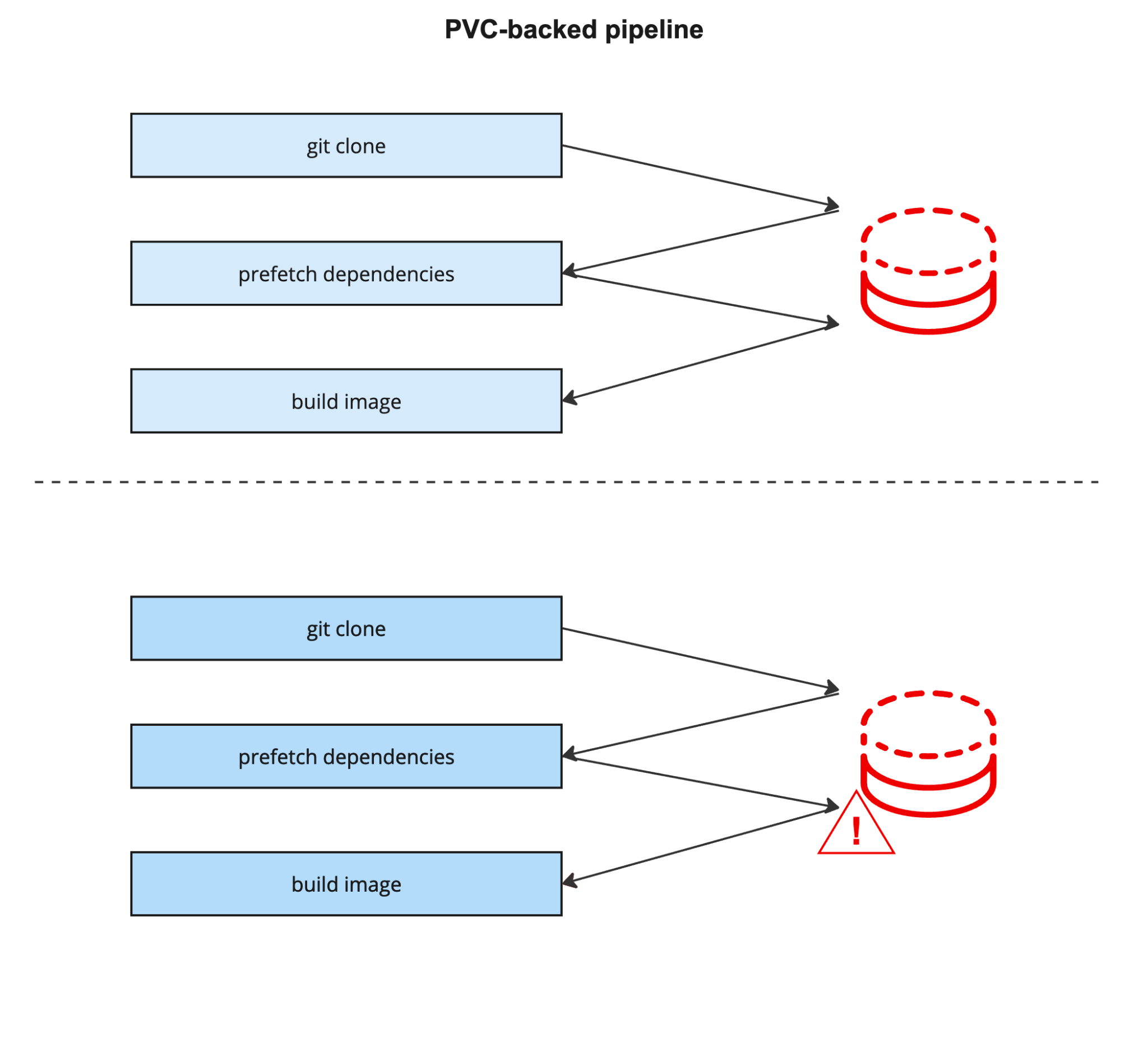
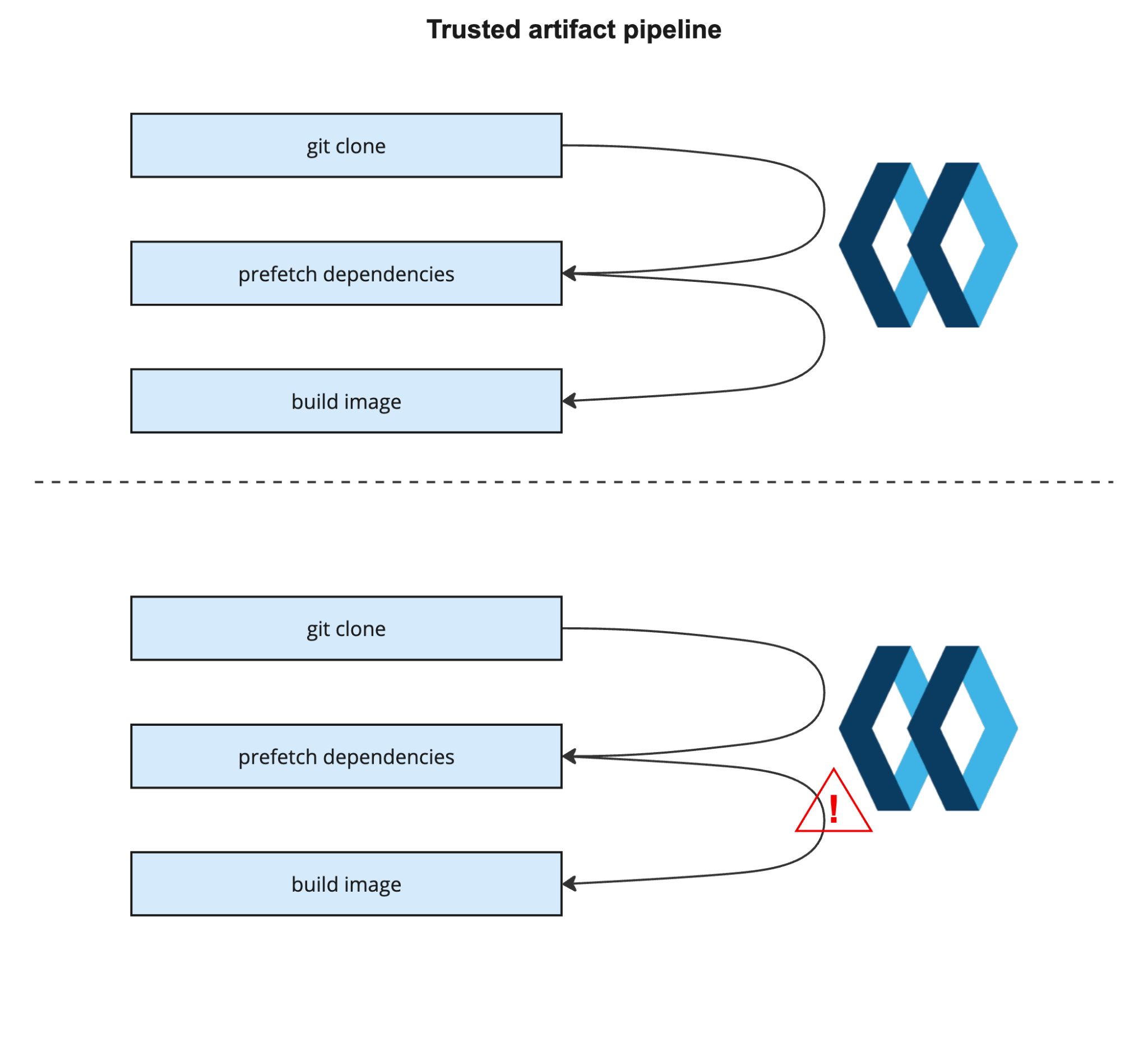
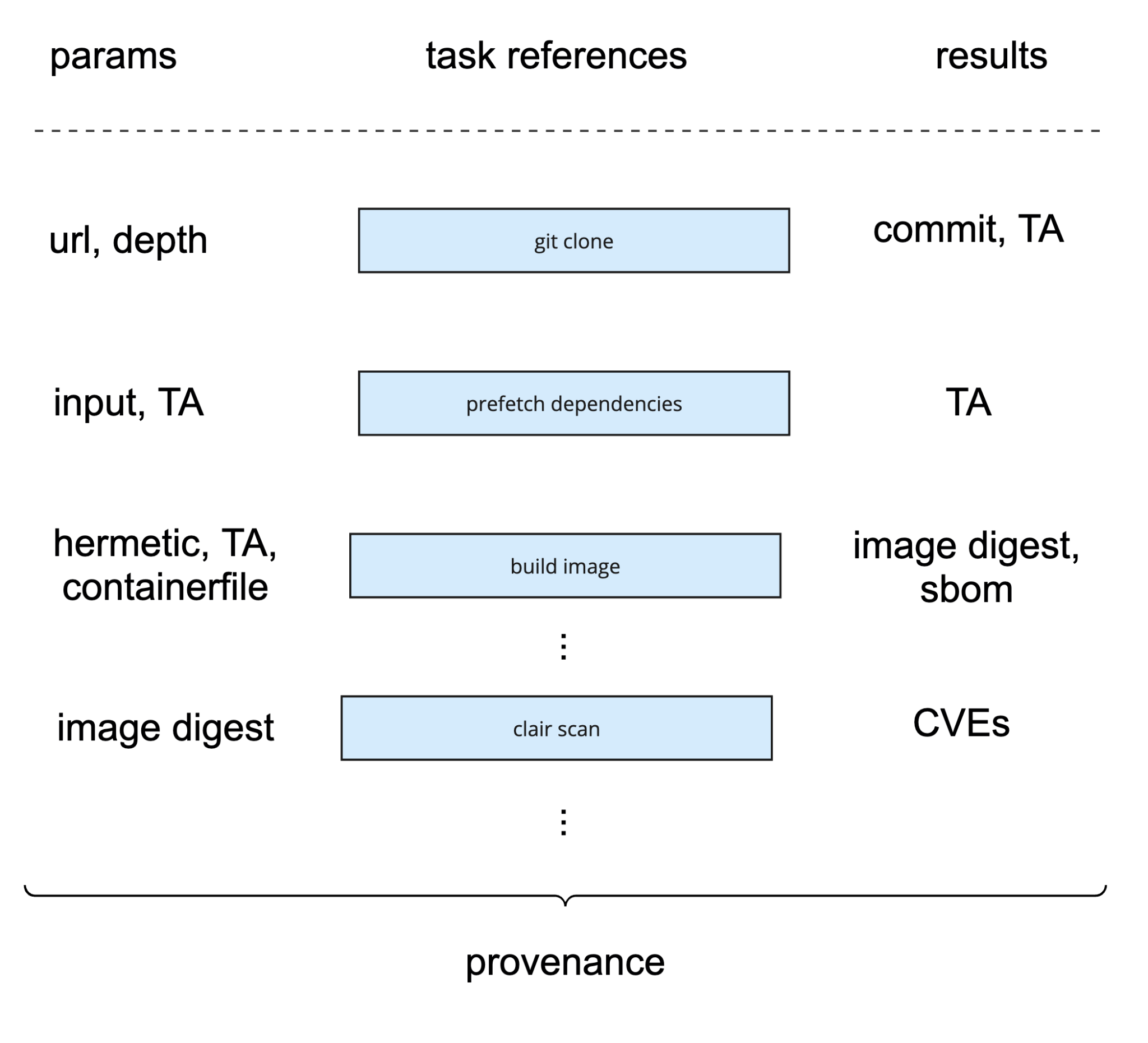
Trusted Artifacts
A method of sharing data between tasks which allows detection of data alterations.
Observer Generated Attestations
Attestations are generated separately from the pipeline (by an 'observer') so they cannot be influenced by the user.
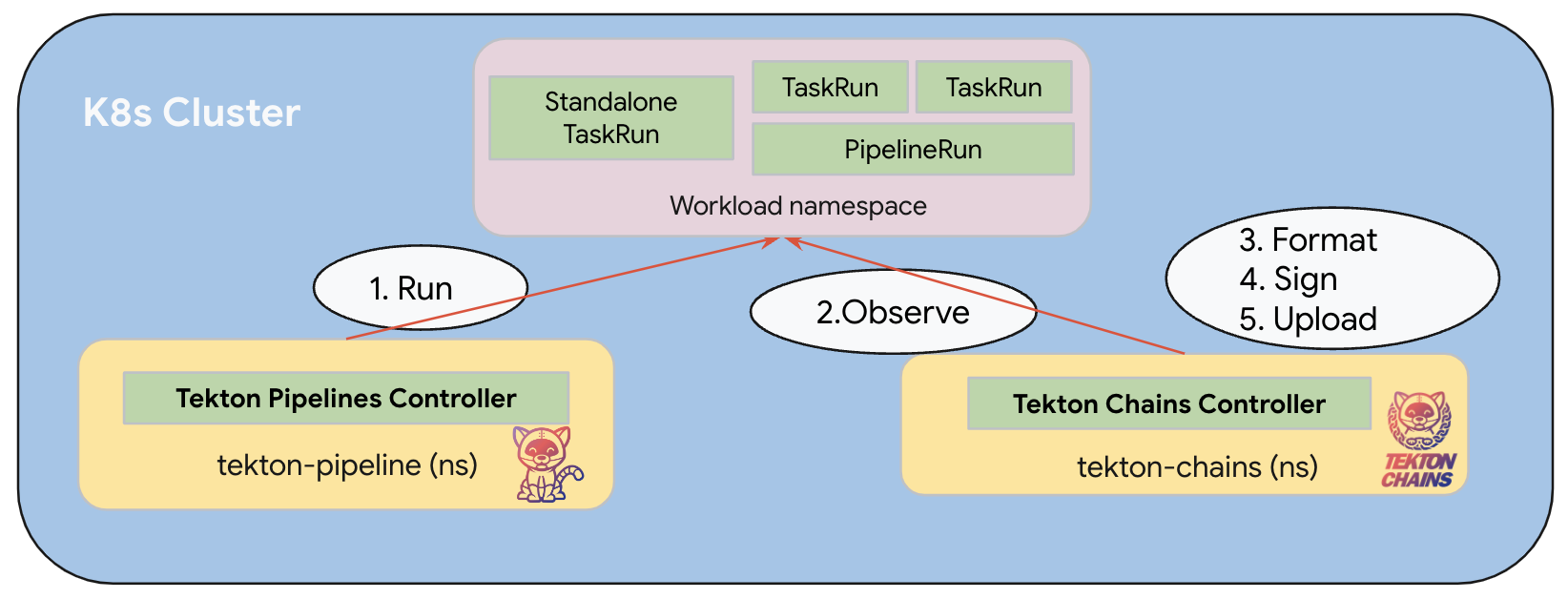
https://tekton.dev/docs/chains/slsa-provenance/#how-does-tekton-chains-work
Policy Engine
A policy engine is used to compare the attestations against required policy (we use Conforma).



Allowed base images

Allowed base images
Release Service
Release service gates access to protected destinations based on policy evaluation.

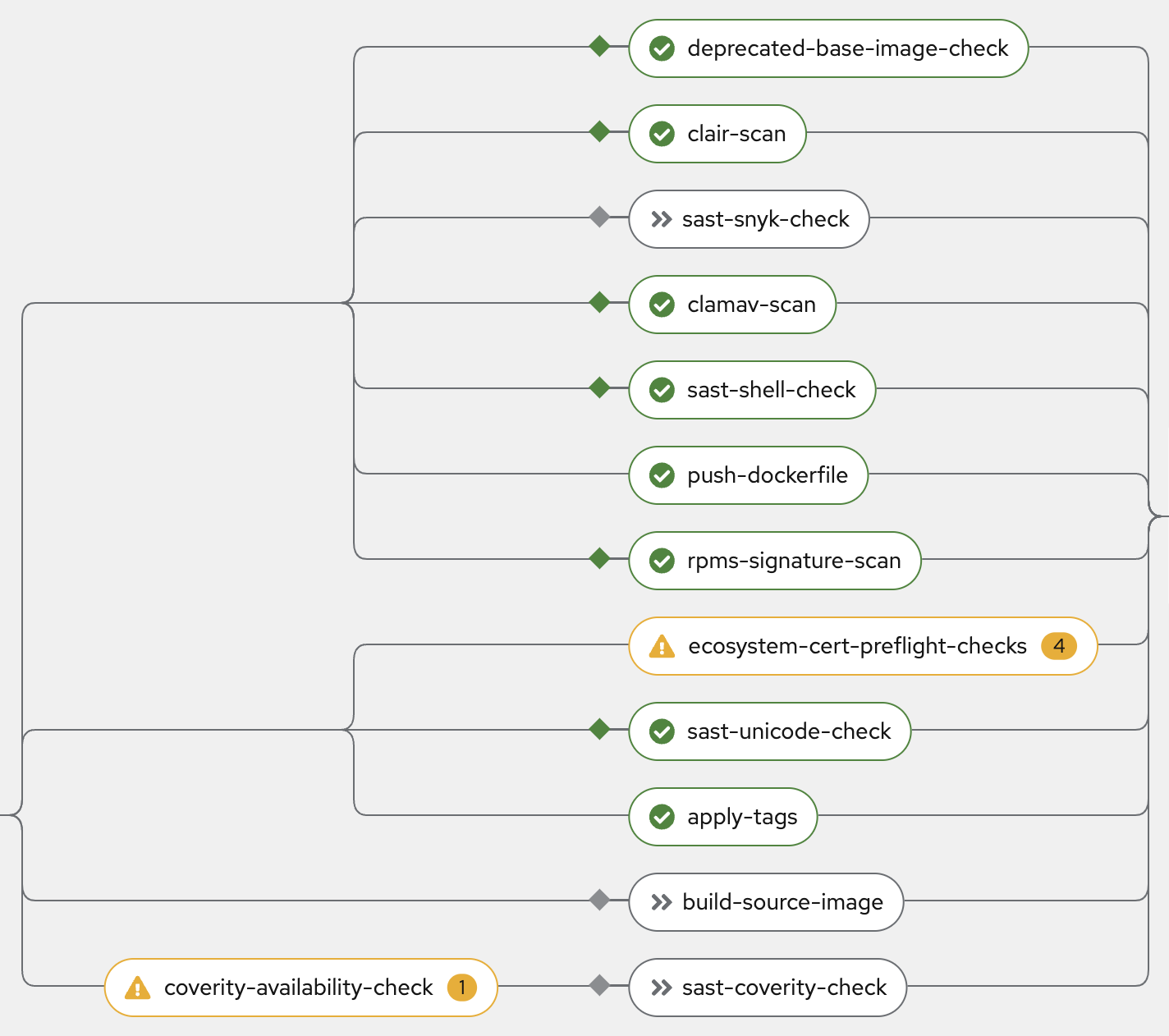
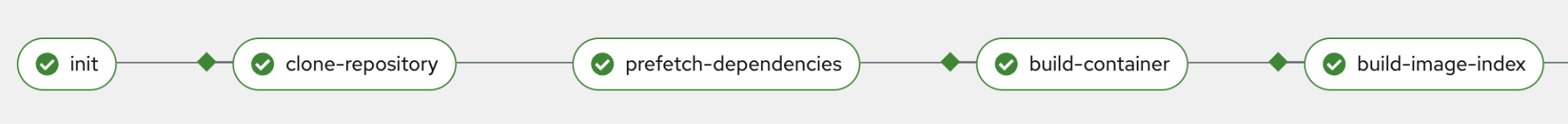
Devs can easily build artifacts
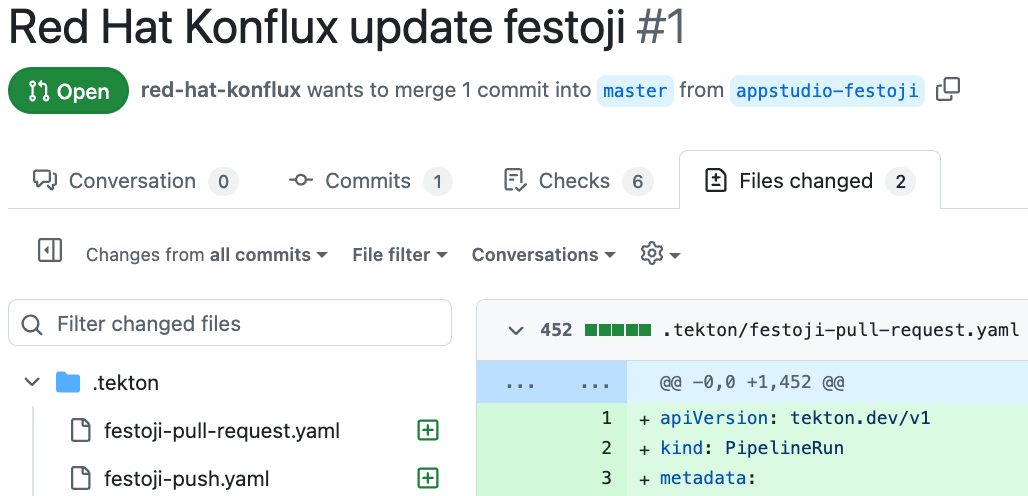
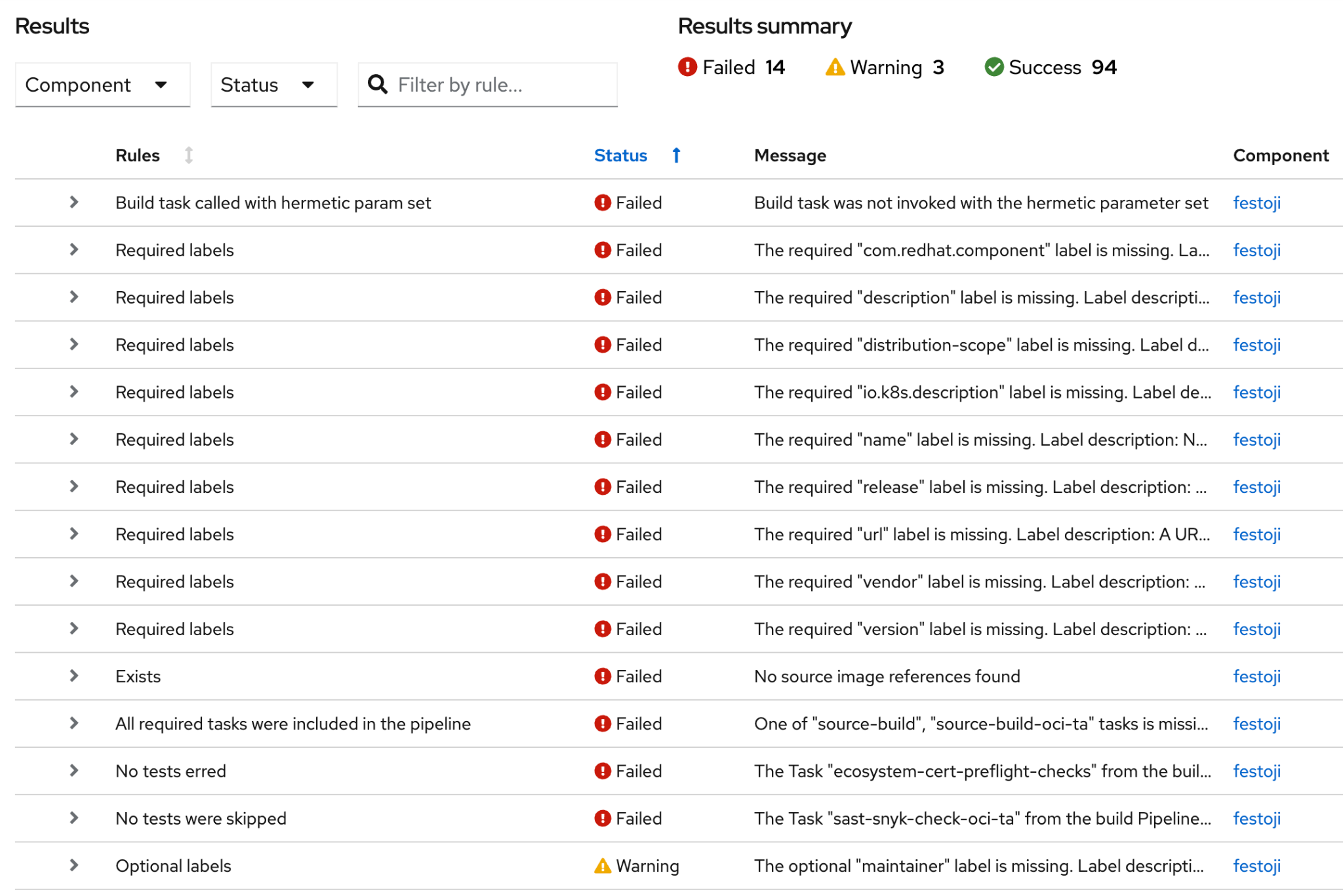
Devs can troubleshoot builds
| __$ oras manifest fetch --pretty quay.io/konflux-ci/tekton-catalog/task-buildah-remote-oci-ta:0.4 | jq .annotations__ |
{
__ “dev.konflux-ci.task.previous-migration-bundle”: ““,__
__ “org.opencontainers.image.description”: “Buildah task builds source code into a container image and pushes the image into container registry using buildah tool.“,__
__ “org.opencontainers.image.documentation”: “https://github.com/konflux-ci/build-definitions/tree/75741ae0dbd0e3ffa0414acc7fbc950740e889ae/task/buildah-remote-oci-ta/0.4/README.md”,__
__ “org.opencontainers.image.revision”: “75741ae0dbd0e3ffa0414acc7fbc950740e889ae”,__
__ “org.opencontainers.image.source”: “https://github.com/konflux-ci/build-definitions”,__
__ “org.opencontainers.image.url”: “https://github.com/konflux-ci/build-definitions/tree/75741ae0dbd0e3ffa0414acc7fbc950740e889ae/task/buildah-remote-oci-ta/0.4”,__
__ “org.opencontainers.image.version”: “0.4”__
}
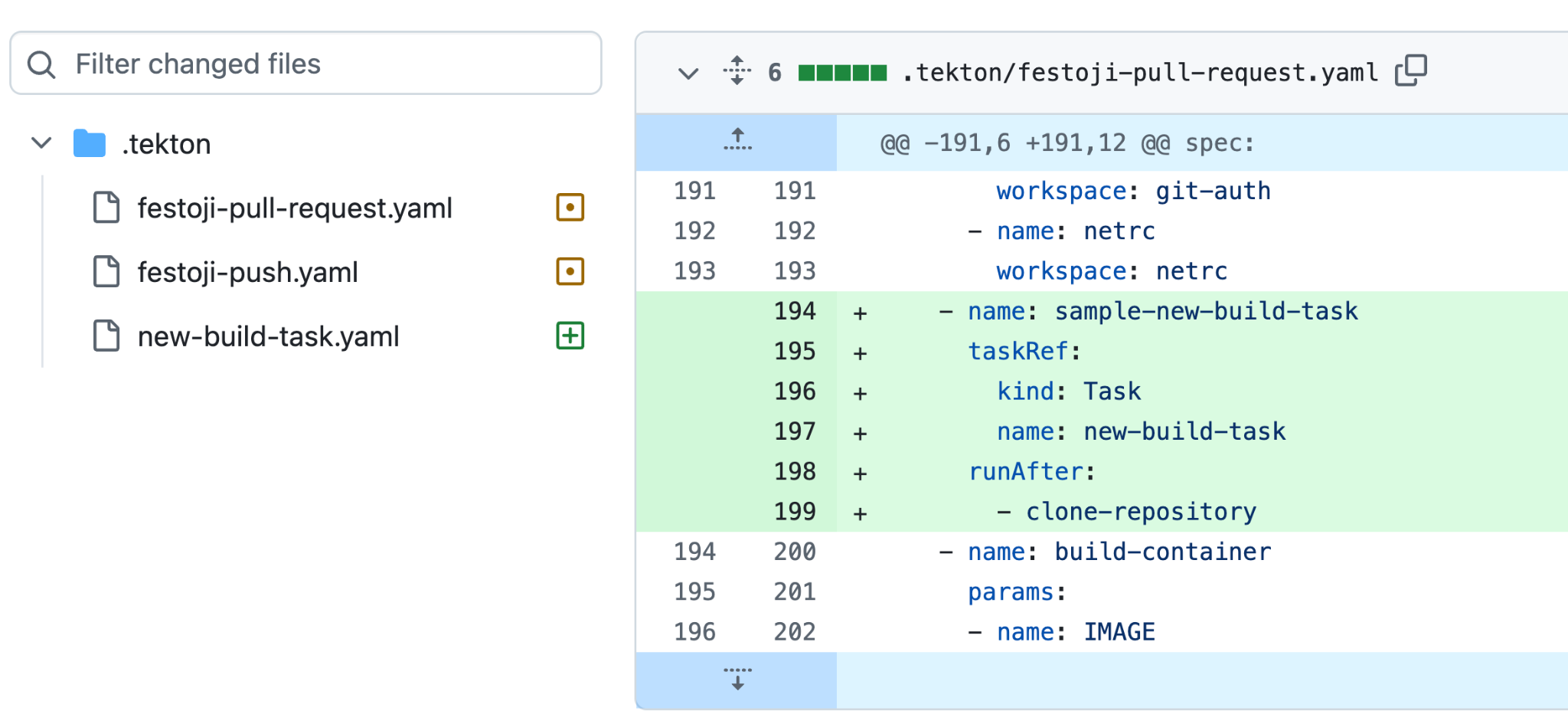
Devs can explore new tech
Devs don’t need to be this unhappy



Thank you!
 @arewm
@arewm