Who Are You Building For: Pipelines Have a Purpose
Andrew McNamara & Julen Landa Alustiza, Red Hat
OpenSSF Community Day North America 2025
Pipelines serve dual purposes
🔒 Security Controls
- Supply chain protection
- Establish organizational trust
- Policy compliance
🛠️ Developer Flexibility
- Customizable workflows
- Innovation enablement
- Community contribution
Pipelines serve dual purposes
🔒 Security Controls
- Supply chain protection
- Establish organizational trust
- Policy compliance
🛠️ Developer Flexibility
- Customizable workflows
- Innovation enablement
- Community contribution

Our Approach: Progressive Trust Model
placeholder
placeholder
placeholder
placeholder
placeholder
K8s + Tekton
Isolated builds
Kubernetes provides RBAC, containerization, and namespace isolation. Tekton provides the pipeline execution framework.
Building Trust: Trusted Task Library
placeholder
placeholder
placeholder
placeholder
Trusted Task Library
K8s + Tekton
Curated and Verified Tasks
Tasks that have been reviewed, tested, and approved for broader use.
- Build process standardization
- Security scanning integration

Building Trust: Trusted Artifacts
placeholder
placeholder
placeholder
Trusted Artifacts
Trusted Task Library
K8s + Tekton
Tamper-Proof Data Flow
Secure artifact sharing between tasks with integrity verification.
- Tamper detection
- Build reproducibility

Building Trust: Observer Generated Attestations
placeholder
placeholder
Observer Generated Attestations
Trusted Artifacts
Trusted Task Library
K8s + Tekton
Independent Verification
Tekton Chains generates signed SLSA provenance separately from the build.
- Unforgeable provenance
- Complete record of build steps
- SLSA Build Level 3
Building Trust: Policy Engine
placeholder
Policy Engine
Observer Generated Attestations
Trusted Artifacts
Trusted Task Library
K8s + Tekton
Policy-Driven Development
Automated policy evaluation guides developers toward compliance.
- Real-time violation feedback
- PR-based policy guidance
- Conforma policy engine

Complete Trust Model: Release Service
Release Service
Policy Engine
Observer Generated Attestations
Trusted Artifacts
Trusted Task Library
K8s + Tekton
Build Once, Release Everywhere
Policy compliance is a required gate before protected releases.
- Environment-specific policies
- Automated release gating

Community Contribution Workflow
Personal Sandbox
→
Establish trust
→
Community Sharing
🧪 Experiment
Start with custom tasks in your own namespace
✅ Promote
Push to trusted task bundles
🤝 Share
Others can leverage your work
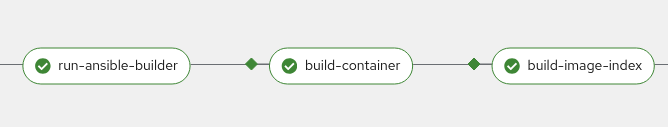
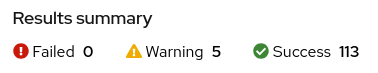
Demo: Customizing the build pipeline
Custom task to build execution environments
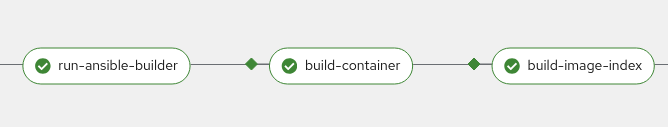
- Policy violations
- Trust model gaps
- Compliance issues

Demo: From Personal Task to Community Asset
Generic Dynamic Containerfile generation
# From specific implementation...
ansible-builder create
buildah build -t $IMAGE context/
# To generalized implementation
exec $MY_SCRIPT
buildah build -t $IMAGE $CONTEXT_DIRECTORY
Benefits of Generalization
- Reusability: Works for Ansible, and other projects
- Trust: No network access and accurate SBOMs during script ensures compliance
- Community: Shared solution benefits everyone
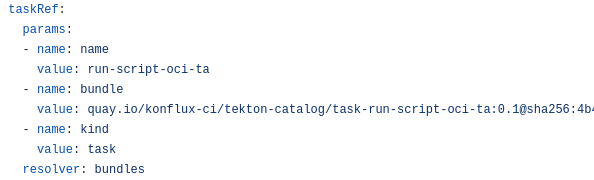
Generic task
# My custom task
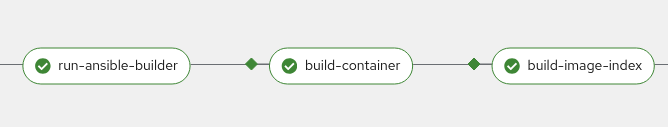
- name: run-ansible-builder
params:
- name: SCRIPT_RUNNER_IMAGE
value: ghcr.io/ansible/community-ansible-dev-tools:latest
- name: SCRIPT
value: ansible-builder create
- name: HERMETIC
value: 'true'
# Later on the pipeline the full reference of the script runner image
# is injected to the SBOM
- name: ADDITIONAL_BASE_IMAGES
value:
- $(tasks.run-ansible-builder.results.SCRIPT_RUNNER_IMAGE_REFERENCE)
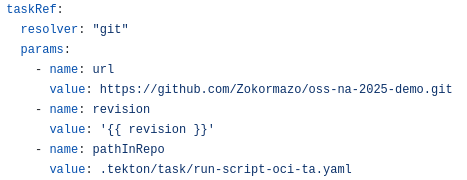
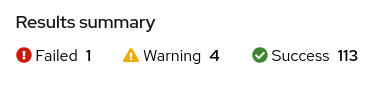
Demo: From Personal Task to Community Asset
Community contributed trusted task
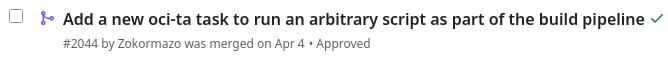
- No more blocking policy violations
- Trust model extended to include this task
- Adheres to policy requirements

Demo: From Personal Task to Community Asset
Reusability
Ansible Execution Environments
Red Hat Developer Hub (Backstage) dynamic plugins
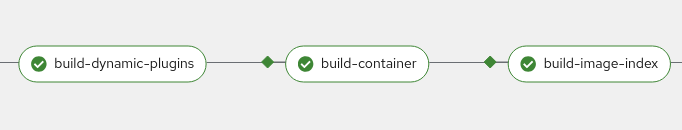
Generic make target
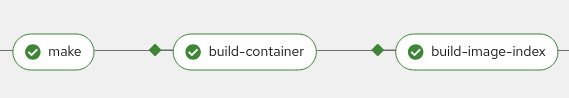
github.com/Zokormazo/oss-na-2025-demo
The Developer Experience
Before Konflux
- Rigid pipeline
- Slow innovation
After Konflux
- Customizable pipeline
- Immediate feedback
- Continuous innovation
- Community task library
Thank you!
 @arewm
@arewm
arewm@redhat.com
 @Zokormazo
@Zokormazo
julen@redhat.com

konflux-ci.dev
hermetoproject.github.io/hermeto
conforma.dev